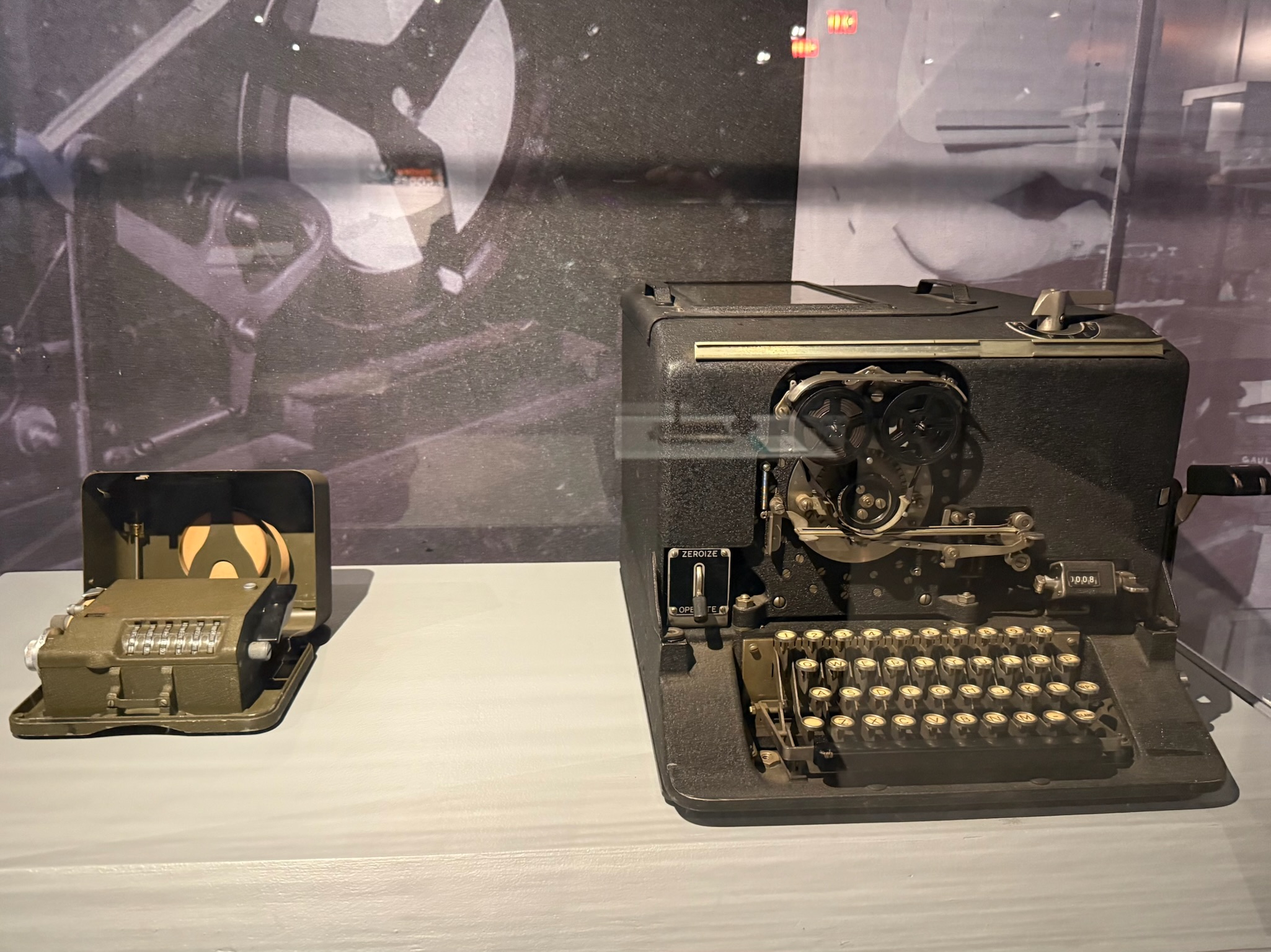
continued... Here were some American machines used in World War II. The little machine on the left was a portable unit. 140,000 were built during WWII. They were also utilized in the Korean and Vietnam Wars, as well. The bigger one to the right was the first production model of an Electric Cipher Machine. The Navy called it CSP-889 (later renamed to ECM Mark II) and the Army called it SIGABA.
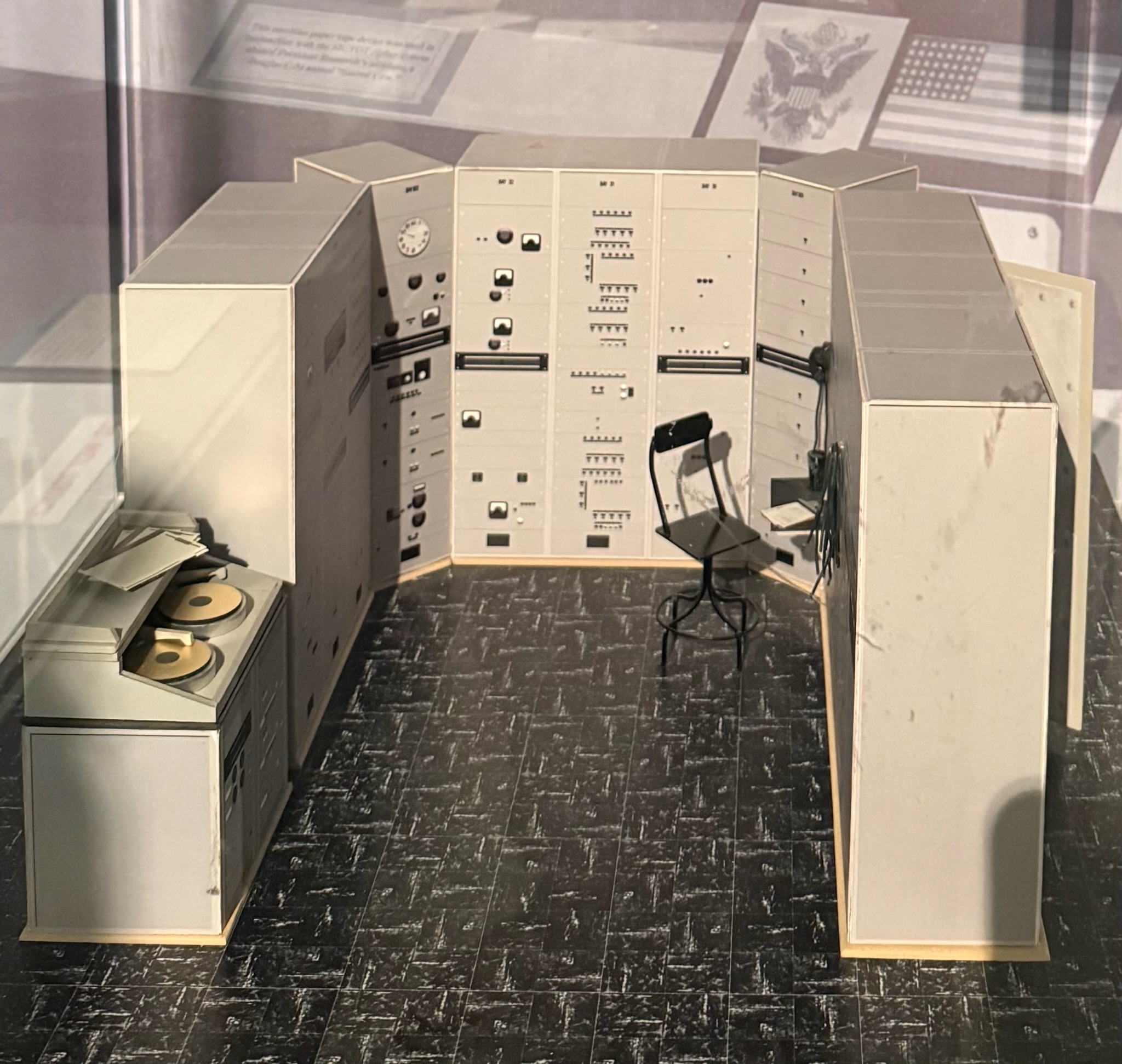
They also could do voice encryption. We believe this was a model of a SIGSALY machine that produced encoded records. There were two turntables that synchronized the sending and receiving ends. When played on a regular record player, they just sounded like random noise. A matching record at the receiving end could unscramble them. They held about 12-minutes of content. They were in service from 1943 to 1946.
There was an exhibit about the Battle of Midway which highlighted how the cryptologists helped to win World War II. In 1942, the US had intercepted an encrypted communication that they were — with great difficulty — able to decipher. It indicated that the Japanese were planning a big surprise attack at AF. The Americans didn’t know where AF was, so they tried a trick. The Americans sent an unencrypted communication saying that Midway Atoll (an island in the Hawaiian island chain that had a US Navy base on it) was short on freshwater. Shortly after, the Americans intercepted an encrypted Japanese communication that the cryptologists deciphered to say that AF was low on fresh water. Ah ha! Since the Americans knew the attack was coming, they were prepared when it happened on June 4. Three aircraft carriers were hidden and lying in wait (we have no idea how one hides an aircraft carrier). Dive bombers from the American ships attacked the Japanese ships and planes, sinking four aircraft carriers and a cruiser, destroying 320 aircraft, and killing more than 3,000 Japanese. This was the turning point of the war with Japan; the Japanese never recovered from this loss. In April 1943, cryptologists deciphered another Japanese communication that had the flight schedule of the Japanese Admiral who had planned the Pearl Harbor attack. On April 18, the Americans assassinated him, kicking off debates about the ethics and legality of targeted assassinations.
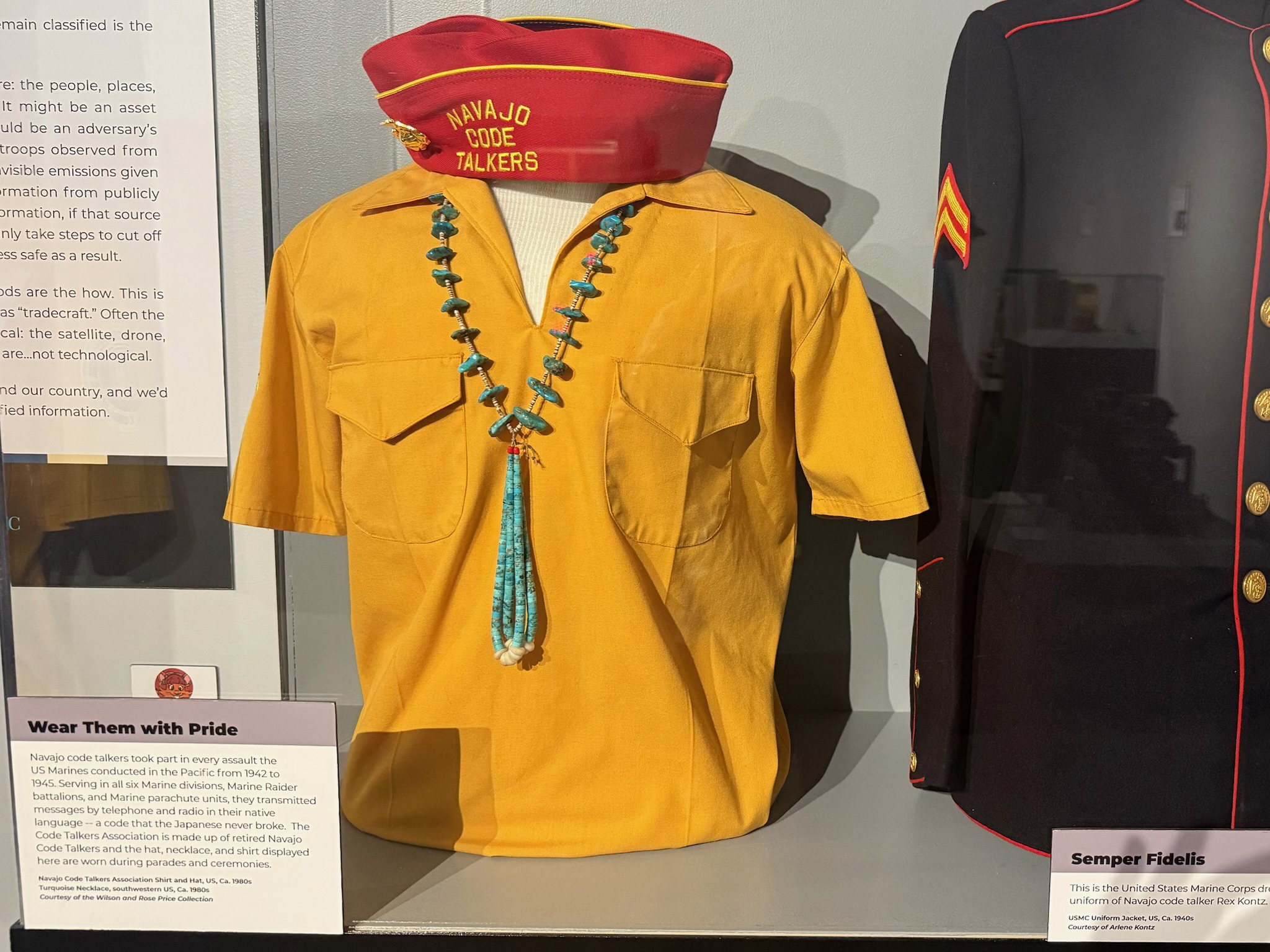
There was a small sign about the Native American code talkers, along with some clothing and a bag from one of the Navajo code talkers. Per this museum, the Native American code talkers had also been used in World War I — if we remembered correctly, the Spy Museum had only mentioned that their indigenous languages had been used for coding messages during World War II.
We were surprised there was no information in the World War II section about the secret cryptology center in Bletchley Park or Alan Turig, the man who broke the German Enigma code. Then we saw a sign that said this was a national museum and thus only focused on how the US/Americans was/were involved. Ah. Bletchley Park was in England and Turig was British.
From 1961 – 1975, there were thousands of people helping with the war efforts in Southeast Asia that were working in various roles involving cryptography. At the height of the conflict in 1969, there were over 10,000 people involved in some aspect of cryptography work.
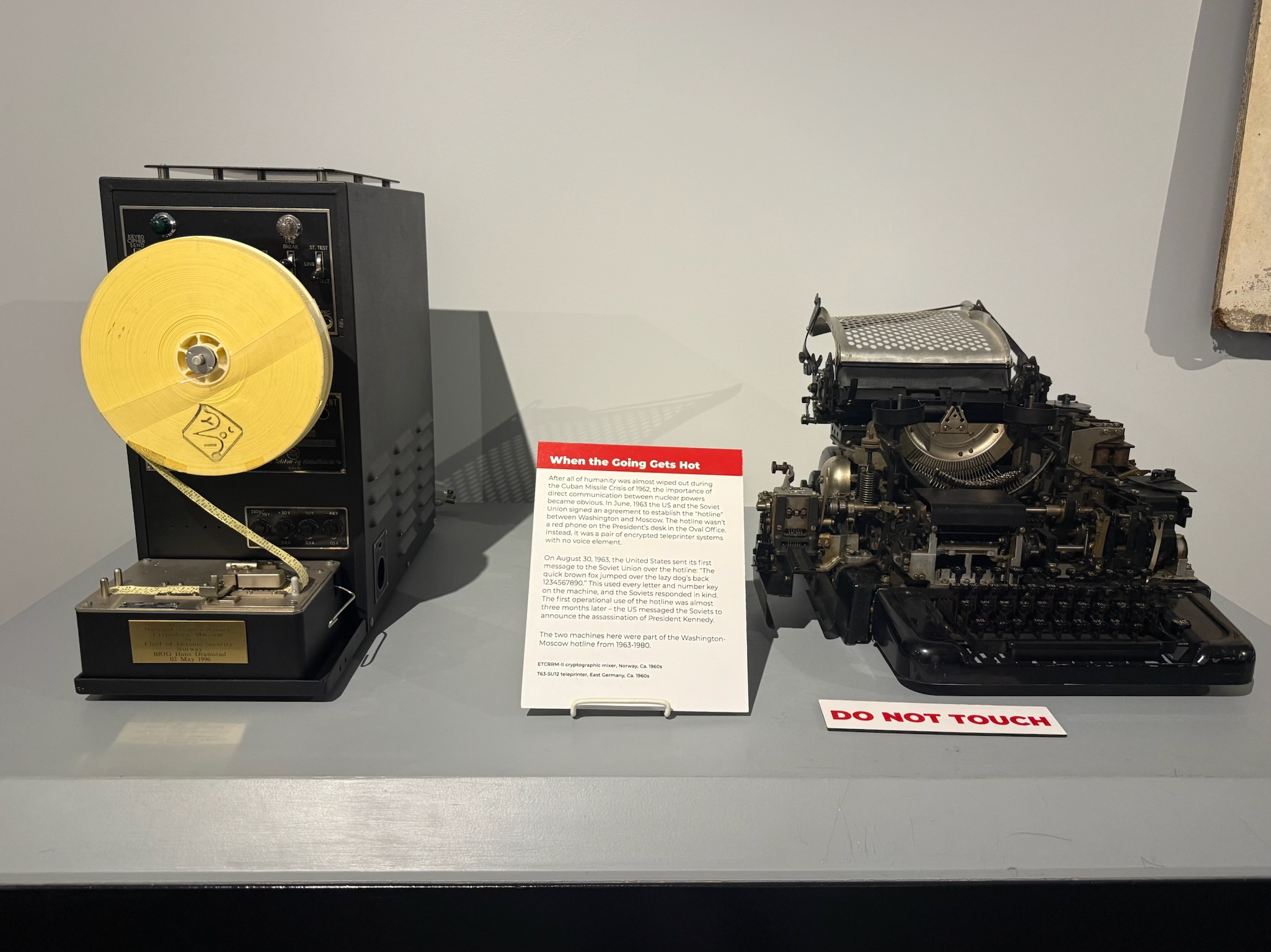
After the Cuban Missile crises in 1962, the Soviets and US agreed to open a direct line of communication. The “hotline” wasn’t a phone, it was a pair of encrypted teleprinter systems with no voice element. Except for the test message to make sure it worked, the first communication was to notify the Soviets of President Kennedy’s assassination. These machines were in use from 1963 – 1980.
These were different generations of secure telephones. The sending unit encrypted the voice calls during transmission and the receiving unit decrypted it, so the message in transit could not be readily understood if intercepted. The one at the top was from the 80s and the one at the bottom began use the 90s and was replaced in 2014.

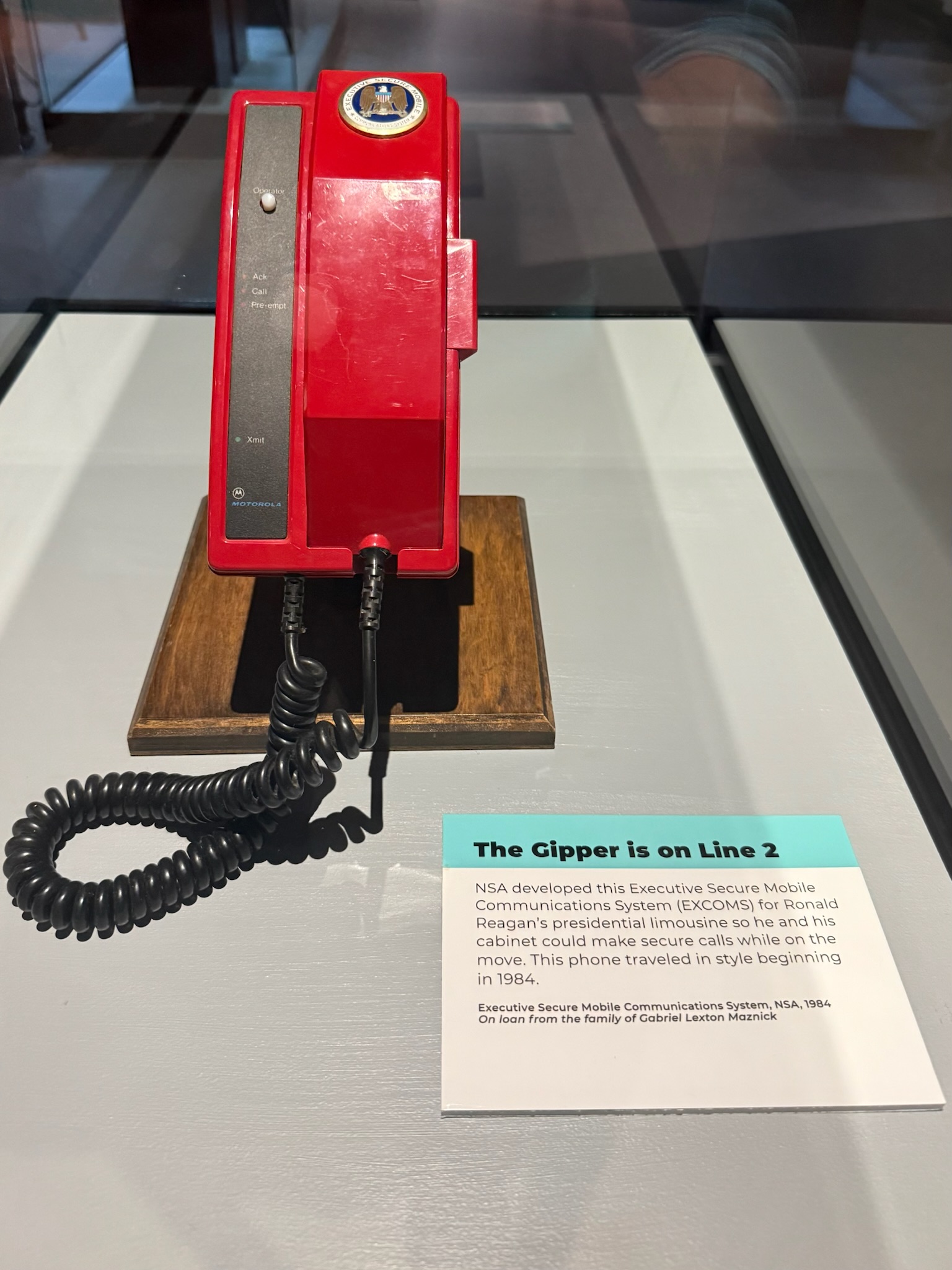
This was the Executive Secure Mobile Communications System (EXCOMS) that NSA developed in 1984 specifically for President Ronald Reagan’s limousine so that the president and cabinet members could make secure calls while on the move.
This was the Miniaturized Integrated Satellite Terminal Equipment (MISTE) or portable satellite station. Weighing only 32-lbs (14.5 kilograms), it provided secure voice and data communications to executives and VIPs.

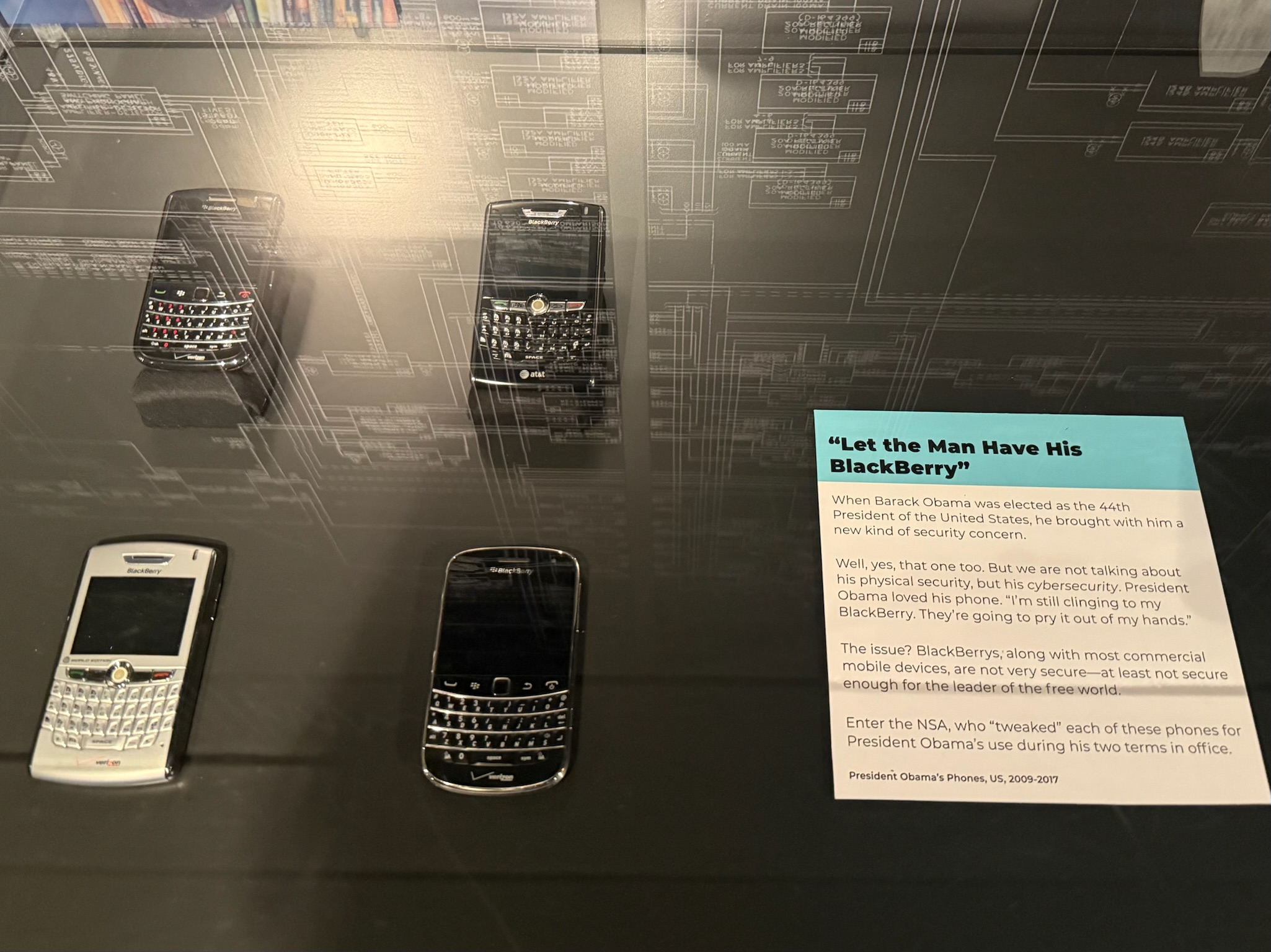
Here were President Obama’s beefed up Blackberries.
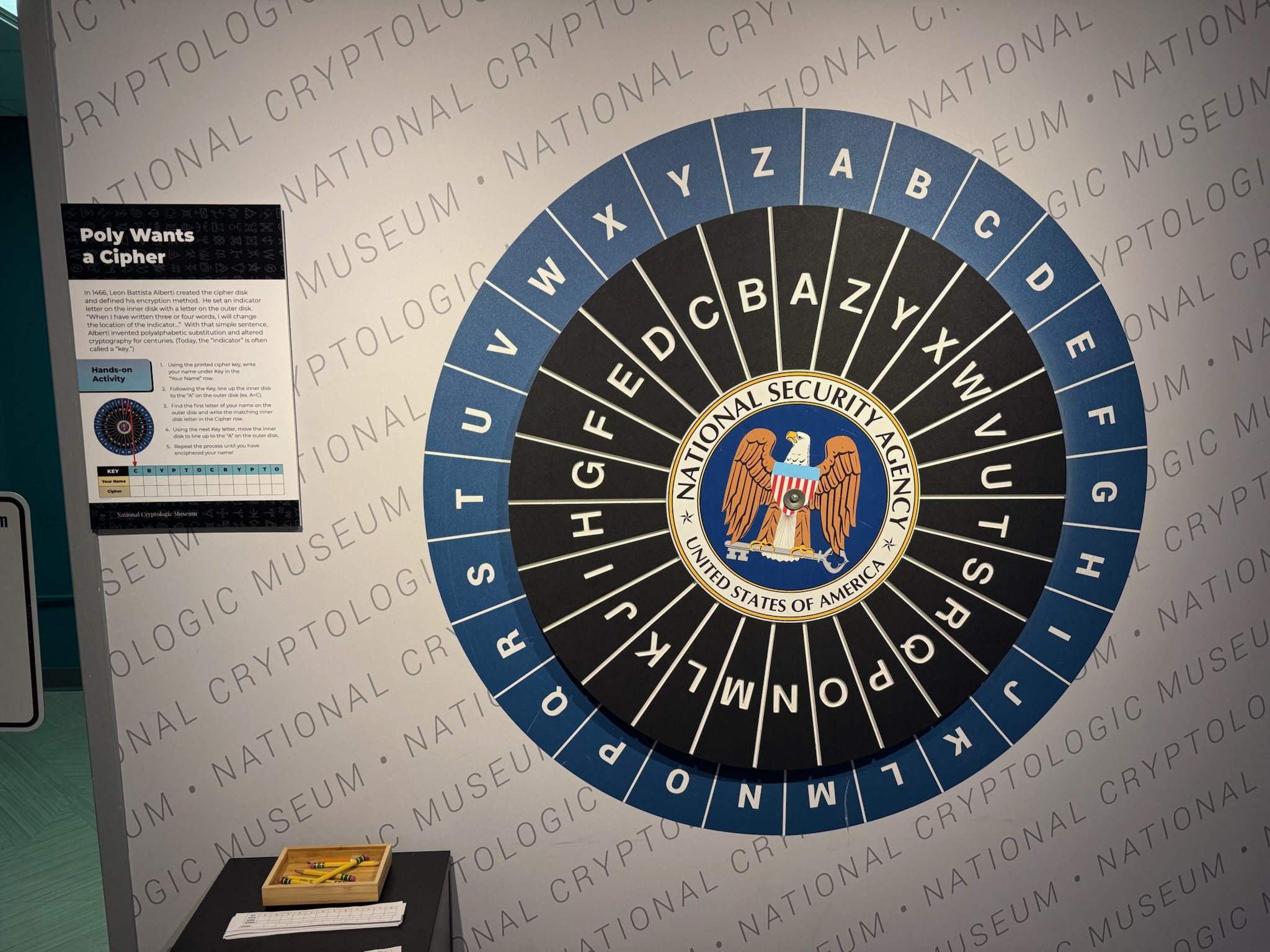
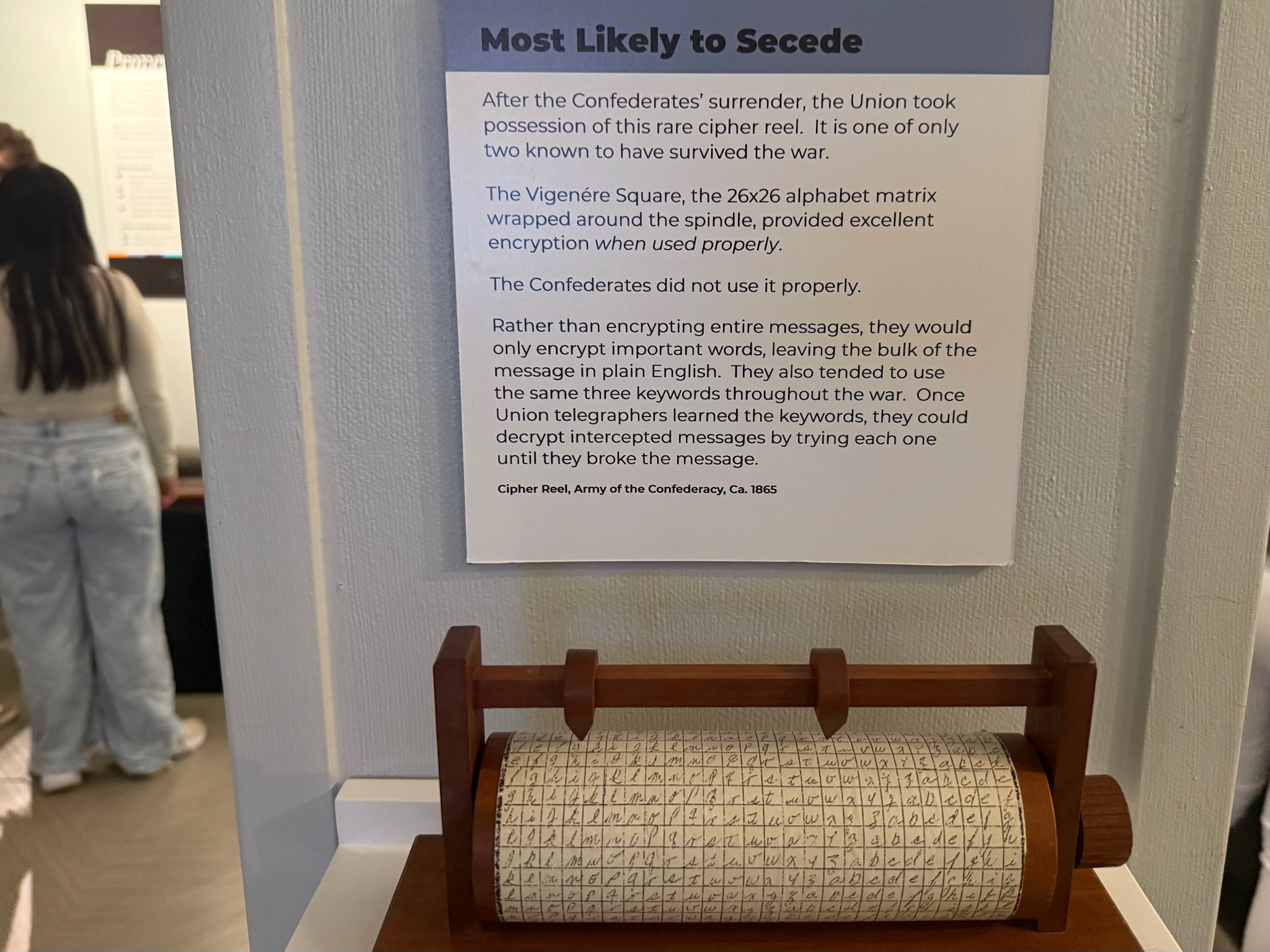
There was an exhibit on encryption tools that predated the creation of the agency in 1917. Ancient tools were mentioned, including the Greek Scytale (where you change the order of the letters in a message), the Roman Caesar Cipher (moving all the letters in the alphabet over by a certain number, so you’d type DEF when your real message was ABC), the Cardano Grille and invisible ink. This cipher disk was created in 1466.
Another cipher mentioned was the Pigpen Cipher (AKA Freemason Cipher) that used a set of symbols to represent each of letters. In 1730, French pirate Olivier Levasseur was captured. Before he was executed, he wrote the location of his hidden treasure in Pigpen Cipher. His treasure has yet to be found, and is estimated to be worth $4 billion in today’s money. Yes, that is a b.

This transitioned into a display on tools used during the revolutionary war and 1800s, including Thomas Jefferson’s Cipher (the one to the left above), with several stories about encrypted message use. One story that was especially interesting was Benedict Arnold. In Yorktown, we’d learned that he was bitter about not being promoted, so to get even, he became a double-agent. He was commanding the fort at West Point, where he was planning to “lose” to the British, but the scheme was caught by the Patriots. Per the sign at this museum, Arnold had sent an encrypted message to British general Sir Henry Clinton offering to sell West Point, the garrison and supplies for 20,000 pounds sterling!
Another interesting story was that Vietnamese prisoners of war (POWs) held at Hoa Lo prison (AKA Hanoi Hilton) developed a tap code, so the prisoners were able to communicate with one another by tapping on the walls.
There was a room devoted to demonstrating how the NSA was at the forefront of the computing revolution; since the 60s they’ve always had the most advanced computers. “As NSA’s intelligence requirements grew, so did their need for computers with more memory and faster processing capabilities. These requirements pushed (and continued to push) computer companies to develop new systems to meet the Agency’s ever-growing demand for innovation.” None of the signs disclosed why their intelligence requirements grew so much, but as we learned at the Spy Museum, it was because they were surveilling Americans (and probably still are).
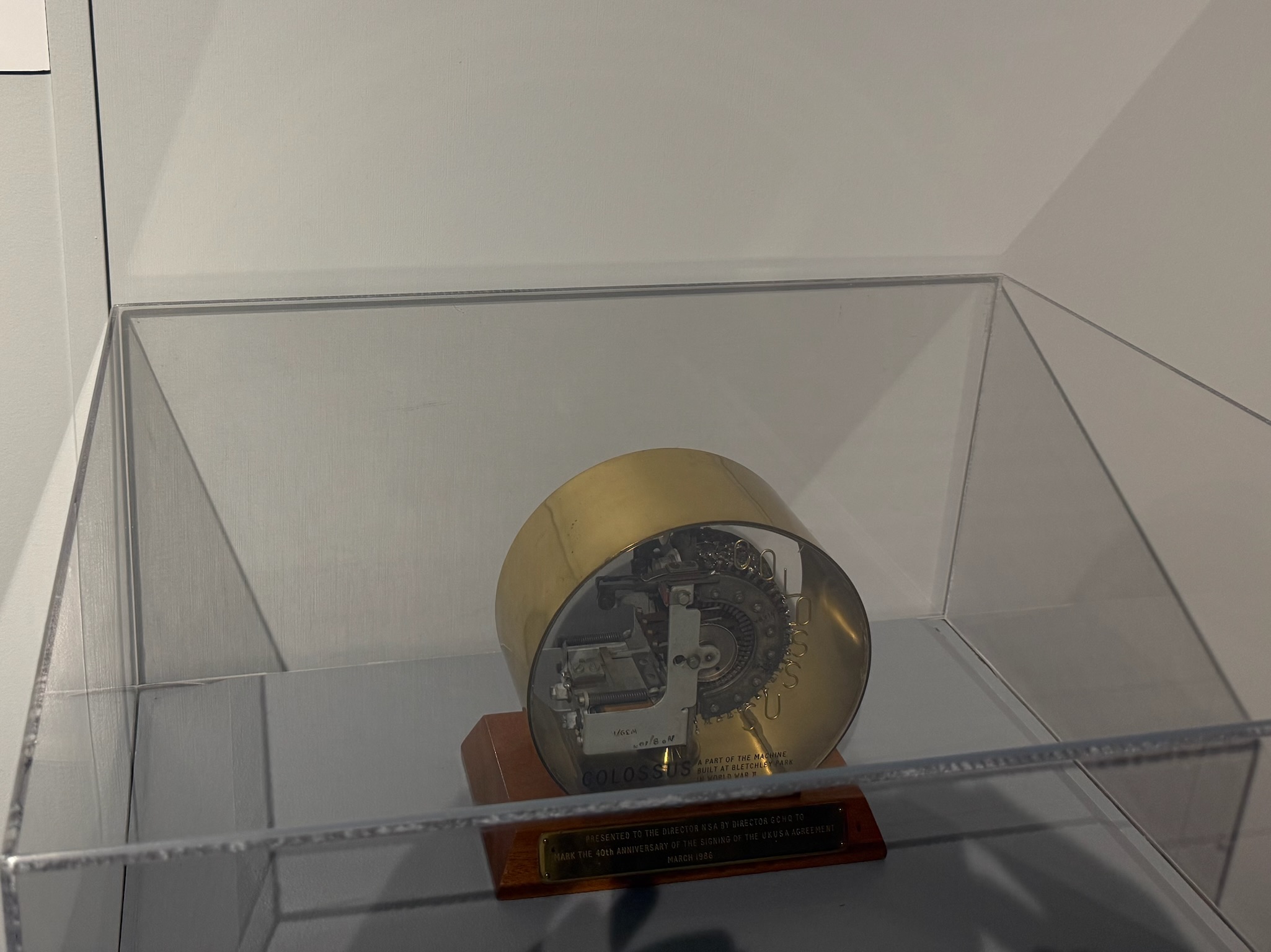
The first electronic computer was build in 1943. It was called Colossus and its purpose was to break the German Lorenz Cipher. Unlike other decrypting machines, Colossus had data storage and retrieval capabilities, parallel processing and variable programming ability.
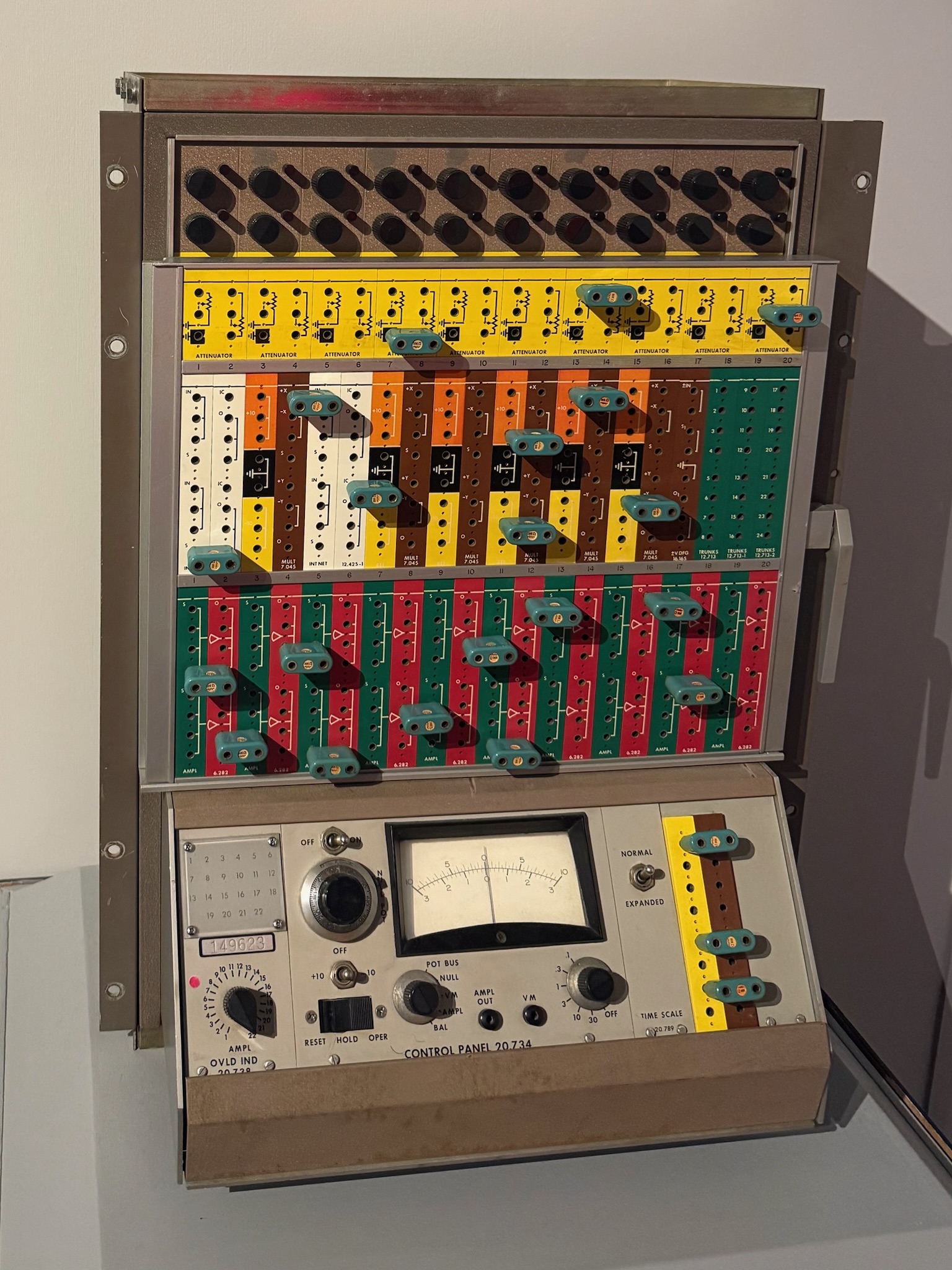
This was the first desktop analog computer used at NSA. It solved mathematical equations. It took an extensive amount of knowledge about mathematics in order to operate.
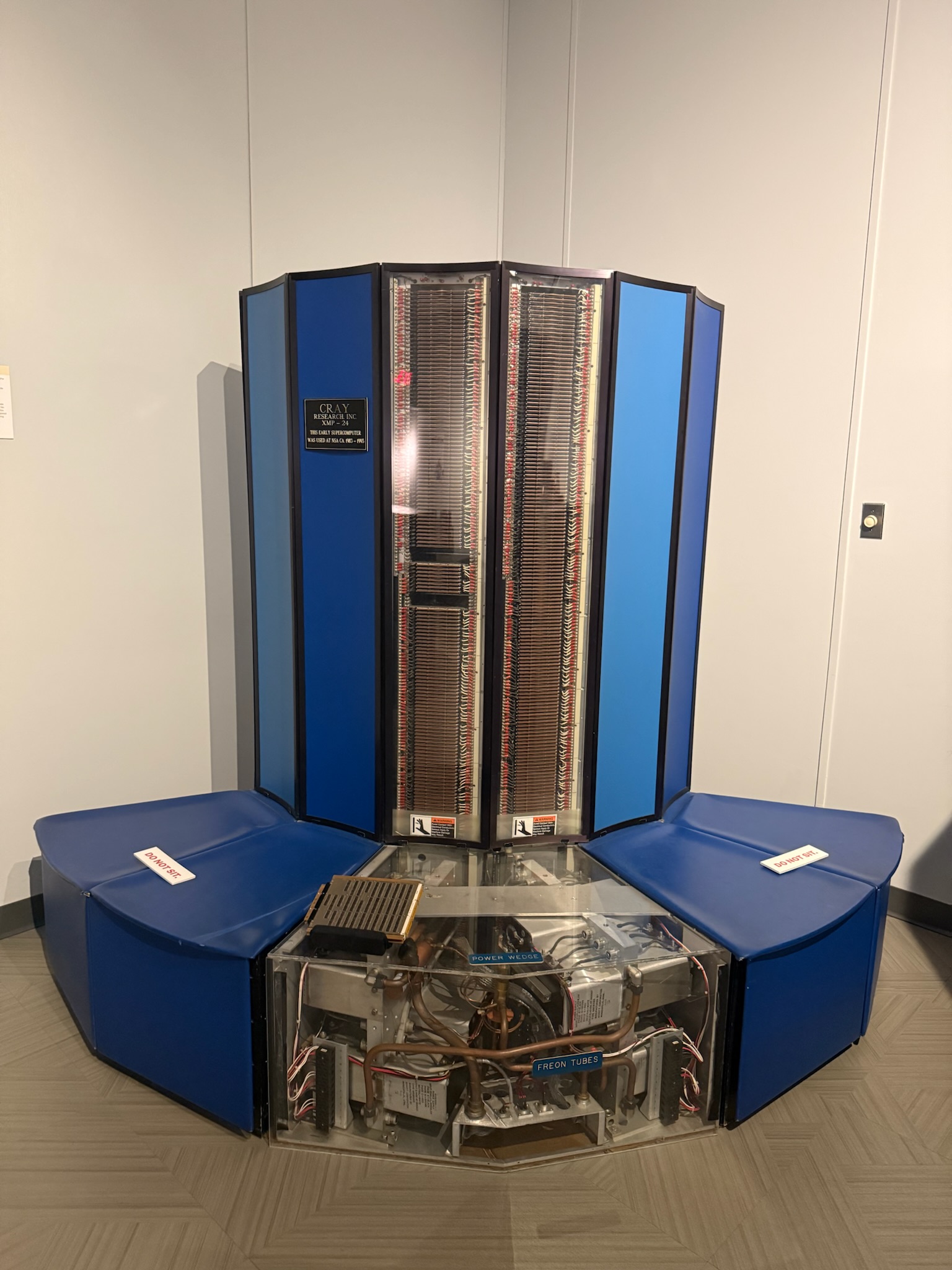
The CRAY X-MP was used from 1983 – 1993. This unit was an upgraded version, delivered in 1987. The CPU had 32-megabytes (MB) of memory, but could be increased to 256 MB. The curved architecture ensured the wires were all shorter and therefore it could process faster. While there was 45.25 miles (72.8 kilometers) of wire in the system, no one wire was longer than 5-feet (1.5 meters). The high processing speed created high heat, and it had to be constantly cooled to prevent it from literally melting down.
In 1985, they also started using the CRAY 2, which was actually a potential bio-hazard for the staff should something go wrong. The unit could get so hot that it would literally melt through the floor, and if the liquid coolant in the innovative immersion cooling system were exposed to fire, it would create a toxic gas. But since it was the world’s fastest and most powerful computer, they decided it was worth the risk. None of the signs said anything about a failure, so we assume all went okay with it.

In addition to the CRAY machines, they were also running The FROSTBURG, which was used by the NSA during much of the 1990s. It was a massive parallel processing computer. It had 64,000 processors that simultaneously worked on different aspects of the problem. It performed 65-billion computations per second.

In 2007, the NSA upgraded to the CRAY “Black Widow,” the most powerful hybrid supercomputer in the world at the time. Its shared memory capacity was up to 16-terabytes (TB) and it stayed cool using turbine fans that pulled cold air from the floor.

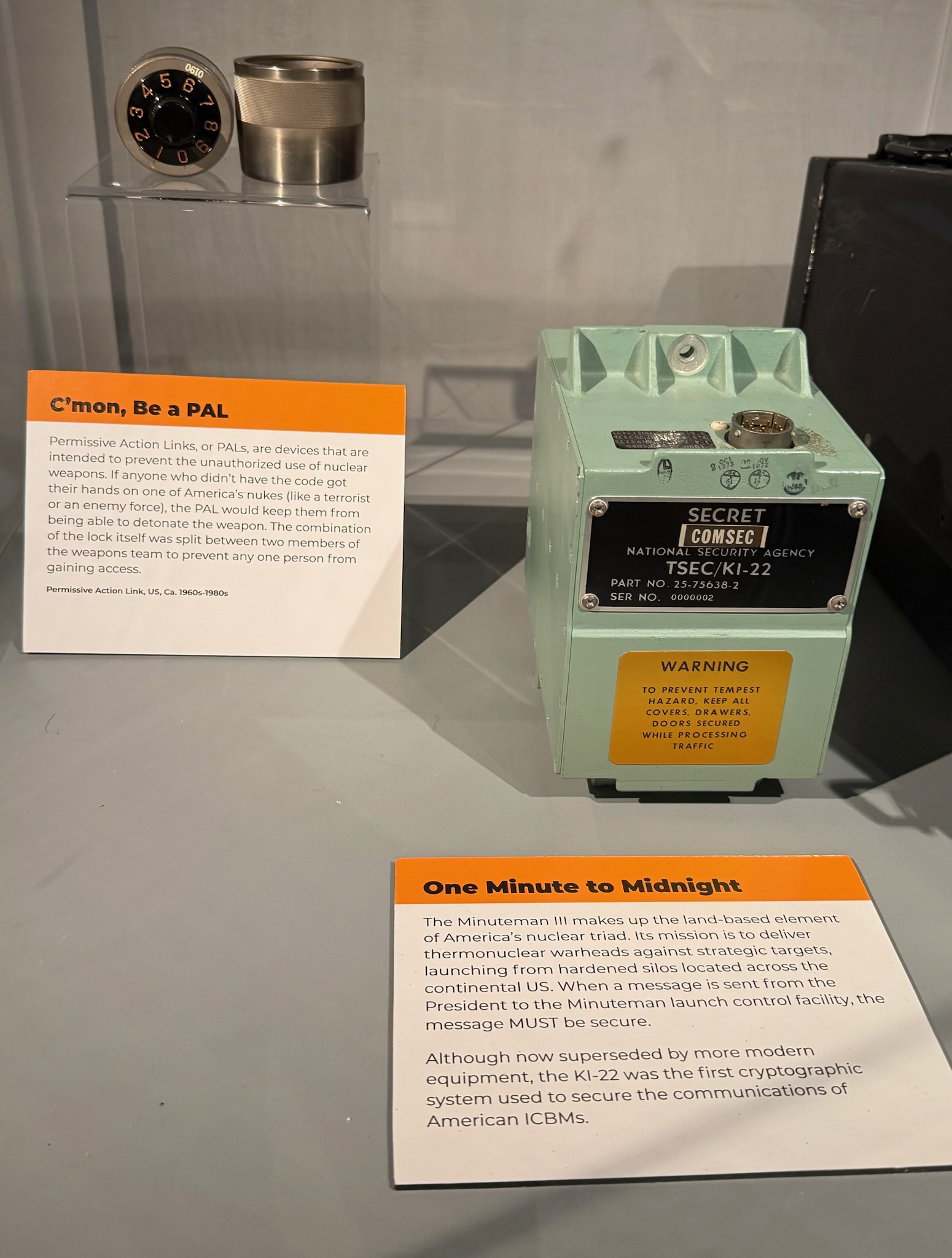
These two systems were the equipment that produced all of the codes in the US nuclear weapons and communications systems. controlled nuclear weapon launches from the late 1980s to the late 2010s. The system in the first photo was called DEC Alpha and was operated by teams of people who worked in pairs. They confirmed that the code really was authorized by the president and created codes to open the PALs on the explosives. The second one was called MP-37 used a different system to ensure the order really came from the president.


The device to the left was the Permissive Action Link (PAL), which was a lock on the weapons. The combination to the lock was sent from DEC Alph and was split between two people so no one person could open the lock by themselves. The item to the right secured communications from the president to the launch control facilities.
This was the device that secured communications between Johnson Space Center in Houston and the orbiting Space Shuttle. The protection of communications was a joint venture with NASA, the Defense Department and NSA. It became operational in 1982 and was used until 2011.

As a side note, many of the signs were obviously written by a millennial or younger. It was kind of fun to read signs that were written more like a text-message or a Twitter/X post than a in proper English. For example, the sign about the lost pirate treasure said “Four. Billion. Dollars. Worth. Of. Pirate. Treasure. It’s still out there. Somewhere.” Another example was the FROSTBURG computer that said “…’Blinky lights’ system.* *Not a technical term (but it should be)”
When we finished up at the museum, Eric said that he was disappointed they didn’t have an exhibit on Peer-to-Peer. Eric hasn’t been to the American History Museum in DC in decades, but he said he remembers the cryptography exhibit there was better than the display at the NCM.
Our assessment of the museum was that it was good overall. Had we gone while we were in Baltimore, when we already had a car and were looking for things to do, we probably would have found it more worthwhile than we did today. We didn’t think it was worth the money for the car rental, nor the hassle of having a car in DC. It also wasn’t worth the drive/time when there were so many other things to do in DC.
We went to lunch at a Thai restaurant called Bankok Kitchen. One of the museum staff had recommended it. It was a few miles away from the museum. The food was really good, though the service was slow because they were short staffed.

The traffic on the drive back to DC was heavy and moved slowly. It took a lot longer to get back than we would have anticipated. Eric dropped Christi and Keith off at The Wharf and returned the car right away. He took the Metro back to The Wharf. We had a quiet night onboard.